So you have the newest, glitziest, "Fisher Price" version of Windows: XP. How
can you use XP in a way that sets you apart from the boring millions of ordinary
users?
The key to doing amazing things with XP is as simple as D O S. Yes, that's
right, DOS as in MS-DOS, as in MicroSoft Disk Operating System. Windows XP (as
well as NT and 2000) comes with two versions of DOS. Command.com is an old DOS
version. Various versions of command.com come with Windows 95, 98, SE, ME,
Window 3, and DOS only operating systems.
The other DOS, which comes only with XP, 2000 and NT, is cmd.exe. Usually
cmd.exe is better than command.com because it is easier to use, has more
commands, and in some ways resembles the bash shell in Linux and other Unix-type
operating systems. For example, you can repeat a command by using the up arrow
until you back up to the desired command. Unlike bash, however, your DOS command
history is erased whenever you shut down cmd.exe. The reason XP has both
versions of DOS is that sometimes a program that won?t run right in cmd.exe will
work in command.com
note : m not comparing bash to dos
DOS is your number one Windows gateway to the Internet, and the open sesame to
local area networks. From DOS, without needing to download a single hacker
program, you can do amazingly sophisticated explorations and even break into
poorly defended computers.
****************
You can go to jail warning: Breaking into computers is against the law if you do
not have permission to do so from the owner of that computer. For example, if
your friend gives you permission to break into her Hotmail account, that won't
protect you because Microsoft owns Hotmail and they will never give you
permission.
****************
****************
You can get expelled warning: Some kids have been kicked out of school just for
bringing up a DOS prompt on a computer. Be sure to get a teacher's WRITTEN
permission before demonstrating that you can hack on a school computer.
****************
So how do you turn on DOS?
Click All Programs -> Accessories -> Command Prompt
That runs cmd.exe. You should see a black screen with white text on it, saying
something like this:
Microsoft Windows XP [Version 5.1.2600]
(C) Copyright 1985-2001 Microsoft Corp.
C:\>
Your first step is to find out what commands you can run in DOS. If you type
"help" at the DOS prompt, it gives you a long list of commands. However, this
list leaves out all the commands hackers love to use. Here are some of those
left out hacker commands.
TCP/IP commands:
telnet
netstat
nslookup
tracert
ping
ftp
NetBIOS commands (just some examples):
nbtstat
net use
net view
net localgroup
TCP/IP stands for transmission control protocol/Internet protocol. As you can
guess by the name, TCP/IP is the protocol under which the Internet runs. along
with user datagram protocol (UDP). So when you are connected to the Internet,
you can try these commands against other Internet computers. Most local area
networks also use TCP/IP.
NetBIOS (Net Basic Input/Output System) protocol is another way to communicate
between computers. This is often used by Windows computers, and by Unix/Linux
type computers running Samba. You can often use NetBIOS commands over the
Internet (being carried inside of, so to speak, TCP/IP). In many cases, however,
NetBIOS commands will be blocked by firewalls. Also, not many Internet computers
run NetBIOS because it is so easy to break in using them. I will cover NetBIOS
commands in the next article to XP Hacking.
The queen of hacker commands is telnet. To get Windows help for telnet, in the
cmd.exe window give the command:
C:\>telnet /?
Here's what you will get:
telnet [-a][-e escape char][-f log file][-l user][-t term][host
[port]]
-a Attempt automatic logon. Same as --l option except uses the currently logged
on user's name.
-e Escape character to enter telnet cclient prompt.
-f File name for client side logging
-l Specifies the user name to log in with on the remote system. Requires that
the remote system support the TELNET ENVIRON option.
-t Specifies terminal type. Supportedd term types are vt100, vt52, ansi and vtnt
only.
host Specifies the hostname or IP address of the remote computer to connect to.
port Specifies a port number or service name.
****************
Newbie note: what is a port on a computer? A computer port is sort of like a
seaport. It's where things can go in and/or out of a computer. Some ports are
easy to understand, like keyboard, monitor, printer and modem. Other ports are
virtual, meaning that they are created by software. When that modem port of
yours (or LAN or ISDN or DSL) is connected to the Internet, your computer has
the ability to open or close any of over 65,000 different virtual ports, and has
the ability to connect to any of these on another computer - if it is running
that port, and if a firewall doesn?t block it.
****************
****************
Newbie note: How do you address a computer over the Internet? There are two
ways: by number or by name.
****************
The simplest use of telnet is to log into a remote computer. Give the command:
C:/>telnet targetcomputer.com (substituting the name of the computer you want to
telnet into for targetcomputer.com)
If this computer is set up to let people log into accounts, you may get the
message:
login:
Type your user name here, making sure to be exact. You can't swap between lower
case and capital letters. For example, user name Guest is not the same as guest.
****************
Newbie note: Lots of people email me asking how to learn what their user name
and password are. Stop laughing, darn it, they really do. If you don't know your
user name and password, that means whoever runs that computer didn't give you an
account and doesn't want you to log on.
****************
Then comes the message:
Password:
Again, be exact in typing in your password.
What if this doesn't work?
Every day people write to me complaining they can't telnet. That is usually
because they try to telnet into a computer, or a port on a computer that is set
up to refuse telnet connections. Here's what it might look like when a computer
refuses a telnet connection:
C:\ >telnet 10.0.0.3
Connecting To 10.0.0.3...Could not open connection to the host, on port 23. A
connection attempt failed because the connected party did not properly respond
after a period of time, or established connection failed because connected host
has failed to respond.
Or you might see:
C:\ >telnet hotmail.com
Connecting To hotmail.com...Could not open connection to the host, on port
23. No connection could be made because the target machine actively refused it.
If you just give the telnet command without giving a port number, it will
automatically try to connect on port 23, which sometimes runs a telnet server.
**************
Newbie note: your Windows computer has a telnet client program, meaning it will
let you telnet out of it. However you have to install a telnet server before
anyone can telnet into port 23 on your computer.
*************
If telnet failed to connect, possibly the computer you were trying to telnet
into was down or just plain no longer in existence. Maybe the people who run
that computer don't want you to telnet into it.
Even though you can't telnet into an account inside some computer, often you can
get some information back or get that computer to do something interesting for
you. Yes, you can get a telnet connection to succeed -without doing anything
illegal --against almost any computer, even if you don't have permission to log
in. There are many legal things you can do to many randomly chosen computers
with telnet. For example:
C:/telnet freeshell.org 22
SSH-1.99-OpenSSH_3.4p1
That tells us the target computer is running an SSH server, which enables
encrypted connections between computers. If you want to SSH into an account
there, you can get a shell account for free at http://freeshell.org . You can
get a free SSH client program from http://winfiles.com .
***************
You can get punched in the nose warning: Your online provider might kick you off
for making telnet probes of other computers. The solution is to get a local
online provider and make friends with the people who run it, and convince them
you are just doing harmless, legal explorations.
*************
Sometimes a port is running an interesting program, but a firewall won't let you
in. For example, 10.0.0.3, a computer on my local area network, runs an email
sending program, (sendmail working together with Postfix, and using Kmail to
compose emails). I can use it from an account inside 10.0.0.3 to send emails
with headers that hide from where I send things.
If I try to telnet to this email program from outside this computer, here's what
happens:
C:\>telnet 10.0.0.3 25
Connecting To 10.0.0.3...Could not open connection to the host, on port 25. No
connection could be made because the target machine actively refused it.
However, if I log into an account on 10.0.0.3 and then telnet from inside to
port 25, here's what I get:
Last login: Fri Oct 18 13:56:58 2002 from 10.0.0.1
Have a lot of fun...
cmeinel@test-box:~> telnet localhost 25
Trying ::1...
telnet: connect to address ::1: Connection refused
Trying 127.0.0.1... [Carolyn's note: 127.0.0.1 is the numerical address meaning
localhost, the same computer you are logged into]
Connected to localhost.
Escape character is '^]'.
220 test-box.local ESMTP Postfix
The reason I keep this port 25 hidden behind a firewall is to keep people from
using it to try to break in or to forge email. Now the ubergeniuses reading this
will start to make fun of me because no Internet address that begins with 10. is
reachable from the Internet. However, sometimes I place this "test-box" computer
online with a static Internet address, meaning whenever it is on the Internet,
it always has the same numerical address. I'm not going to tell you what its
Internet address is because I don't want anyone messing with it. I just want to
mess with other people's computers with it, muhahaha. That's also why I always
keep my Internet address from showing up in the headers of my emails.
***************
Newbie note: What is all this about headers? It's stuff at the beginning of an
email that may - or may not - tell you a lot about where it came from and when.
To see full headers, in Outlook click view -> full headers. In Eudora, click the
"Blah blah blah" icon.
****************


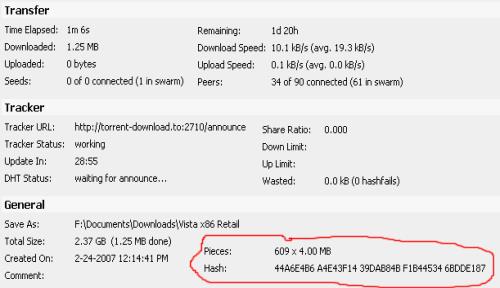
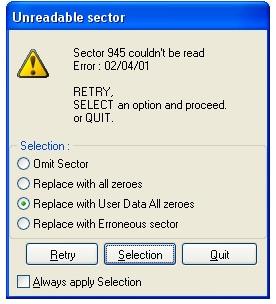 Corrupted *.ISO Image File
Corrupted *.ISO Image File